The Hidden Payment Security Risks in Stadium Self-Service Kiosks

Sports will never be unpopular, regardless of where you go across the US. Therefore, it’s unsurprising that many stadiums have leaped into offering efficient self-service kiosks to help fans get their tickets quicker and easier than ever before.
However, with this convenience, there are high risks to cardholder data. Consider that kiosks are public-facing and often left unattended and unwatched by personnel. That means, even with the best intentions, there are plenty of opportunities for hackers and data thieves to skim cards, tamper with machines, and even use internal connections (such as stadium WiFi) to launch attacks.
There’s a reason why even leading US data carriers warn football fans to stay away from stadium WiFi (and it’s not even to do with marketing).
Ultimately, self-service kiosks often go underexamined at stadiums, and there are plenty of reasons why business owners should pay closer attention and protect their customers’ data.
Why Stadiums Are Relying on More Self-Service Kiosks Than Ever
The benefits of self-service kiosks in stadiums are fairly obvious. They help to reduce lines, they get fans to their seats faster, and they make life more convenient for customers. Above all, they improve game day experiences, and also help to boost revenue and return rates for stadium owners.
Contactless payments and self-service, too, have become part of the everyday norm since the pandemic. Across retail in general (and we can apply the same logic to stadium sales), studies show the majority of US consumers now prefer self-service to staffed service.
However, it’s easy for stadium owners to get swept up in the fever of providing a more efficient service, potentially overlooking vital card security measures established under PCI DSS, which defines the PCI compliance requirements for handling cardholder data. Security hardening, however, shouldn’t be an afterthought or a benefit, rather, it should always be a crucial checkpoint on the way to deploying new kiosks (and maintaining them over time).
The Common Weak Points Inside Self-Service Kiosk Hardware
The weakest, most exploitable points that hackers can access within self-service kiosks will vary from case to case. However, some of the most glaring issues may include:
- Card terminals and pads that are poorly protected against tampering and skimming
- Third-party payment processing software and peripherals that haven’t been carefully vetted for security standards
- Physical, open ports hackers can use to insert malware drives into (e.g., open USBs)
- Too many programs or vendors operating within one machine (leading to confusing maintenance checks)
- Lack of physical monitoring and poor access controls (e.g., no password access systems or default access codes)
- Legacy software or programs that are no longer patched (such as outdated operating systems like Windows XP!)
- Poorly secured physical access to kiosks (e.g., kiosks from the same manufacturer often use the same lock, so one key can open them all.)
Network and Software Risks Stadium Teams Often Overlook
In addition to the common weak points listed above, stadium teams may also overlook the following when deploying self-service kiosks, effectively reducing the robustness of their security and increasing the risk of cardholder data leaking:
- Unencrypted data channels and connections to poorly-secured endpoints (such as WiFi routers with default security and weak password controls)
- Zero patching and updating schedules; merely rolling out hardware and expecting it to provide a service
- Flat networking and data storage (i.e., zero segmenting to separate sensitive data and access points from public attacks)
- Simple misconfigurations in code that can allow hackers easy access to internal systems and sensitive data
- Shadow IT (systems and devices connected via kiosks without IT oversight or approval)
Simply avoiding software patches and updates could result in hackers exploiting kiosks for extensive cardholder information, putting stadiums at risk of reputational damage, lawsuits, and heavy penalties.
How High Foot Traffic Makes Stadiums a Target for Payment Fraud
Attackers prioritize stadiums for several reasons, one of the main being that they attract millions of fans and millions of dollars in revenue every year. Huge venues like the Allegiant Stadium, Las Vegas, for example, made hundreds of millions of dollars in the past year alone.
With high foot traffic, too, attackers can be stealthy and opportunistic. Blending in and working at speed, experienced fraudsters can skim cards, insert malware, and steal data as stadium security teams focus largely on keeping masses of people physically safe on game day.
Even lower-attendance NFL games frequently welcome more than 50,000 people. Imagine how easy it is for attackers to hide at bigger games (and consider that there is always a steady stream of marks to attack).
Beyond high traffic, however, stadiums are at further risk thanks to the time pressures they face to get kiosks up and running, potentially missing essential security checks. There’s also the issue of training and shared knowledge. At stadiums reliant on seasonal intake, for example, staff may vary from one quarter to the next, meaning security knowledge may not be shared between everyone on the team.
Practical Steps Stadium Operators Can Take to Keep Kiosks Safe
Keeping kiosks safe at stadiums is a long-term issue that requires careful security strategizing. Here are a few practical steps to take along the way:
- Carefully audit all software vendors used for kiosks (and only partner with what’s necessary)
- Follow PCI DSS v4.x data security standards and physically fortify kiosks as their own payment endpoints
- Ensure all data shared and stored is encrypted
- Make security hardening an essential part of the kiosk rollout process (and establish clear, regular maintenance checks)
- Patch software regularly and draw up dedicated incident response plans
- Apply secure access controls, consider biometrics, and avoid unsecure IT
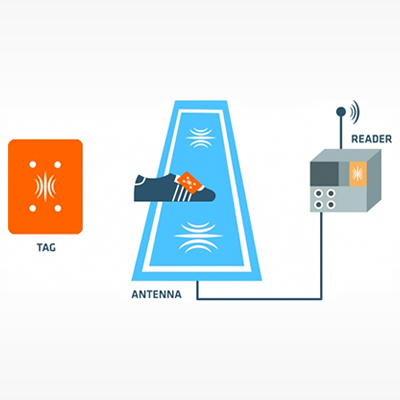
- Install additional, physical security monitoring, such as sensors and cameras
- Carefully train all personnel on kiosk security handling and monitoring
- Use tamper-resistant hardware
- Segment all your connections and ensure specific security tasks are delegated to IT, operations, and security teams
With stadium attendance unlikely to slow down any time soon, businesses need to do more, right away, to keep their fans’ card data safe. The tips listed above are just the start, with working closely with cybersecurity professionals always recommended.